-
Gallery of Images:

-
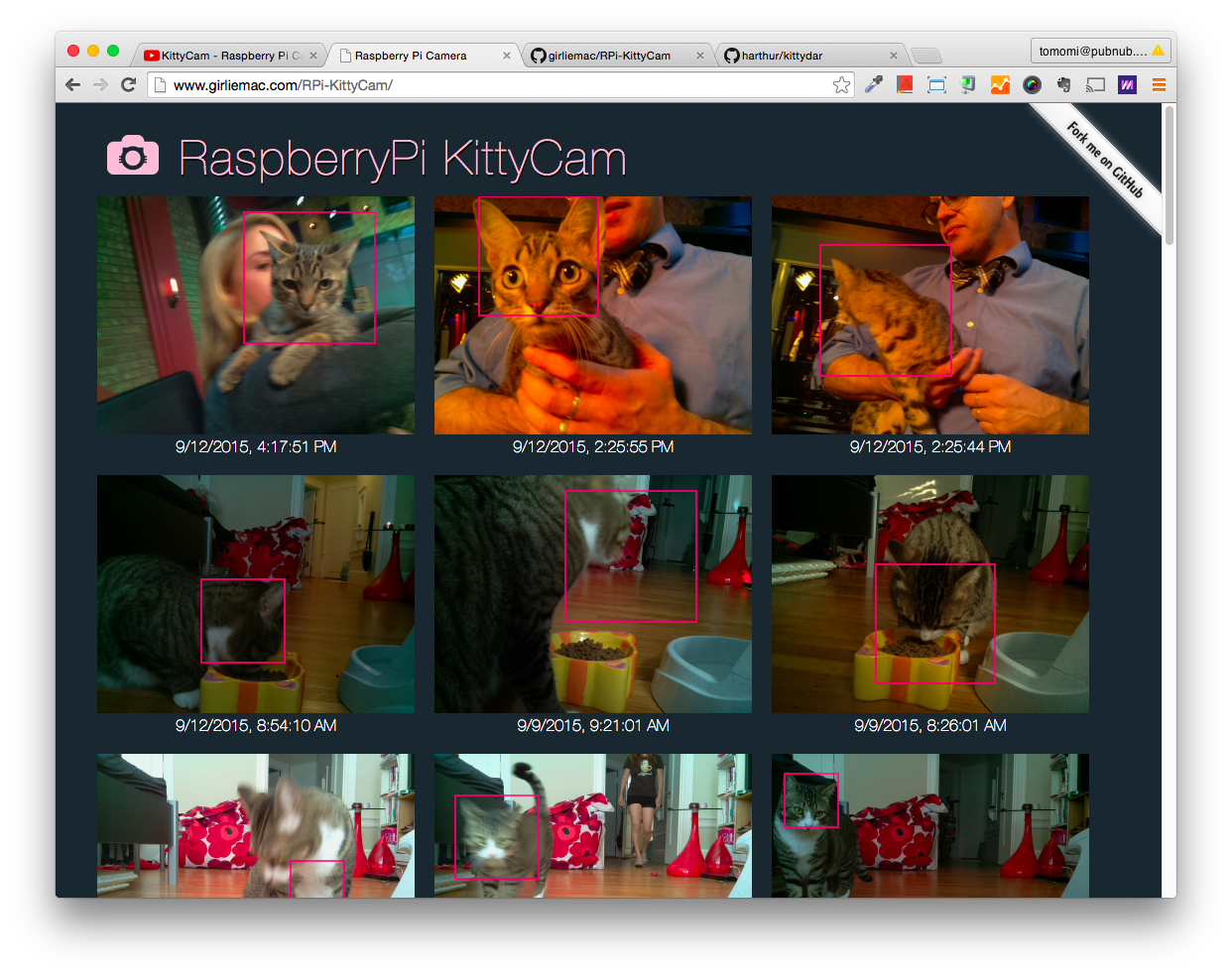
The hacking market inside the deep web is flourishing thanks to the anonymity offered by the communications protocols implemented in this part of the web. The newest trend observed by security experts is the model of sale known as hacking as a service. HACKER HIDE THEIR INDENTY BY USING TOR AUR DARK WEB. Hacking and Coding tutorial August 9, 2017. We offer the latest hacking news and cyber security courses for ethical hackers, penetration testers, IT security The hacking tutorial for today is about 3 Steps GMail MITM Hacking Using Bettercap. Computer security is improving and getting tough day by days, but most of technology leave the users behind about the importance of awareness of the user itself. By buying tools and tutorial materials which are not only expensive but also difficult to find sellers and modders selling the updated version, because hacking is pretty much about building tools and malwares to detect loop holes in your target system. GBHackers on Security is Advanced Persistent Cyber Security Online platform which including Cyber Security Research, Web Application and Network Penetration Testing, Hacking Tutorials, Live Security Updates, Technology updates, Security investigations With dedicated Cyber security Expert Team and help to community more secure. 0x0 Exploit Tutorial: Buffer Overflow Vanilla EIP Overwrite. 0x2 Exploit Tutorial: Web Hacking with Burp Suite. 0x3 Exploit Tutorial: Buffer Overflow SEH Bypass Hacking is a term with a wide variety of acts associated with it. Some are incredibly complex and demand a high degree of knowledge, others are little more than installing some software on your device and acting a bitless than ethically. Our tutorial for today is How to Install SugarCRM on Centos 7 in Simple Steps. SugarCRM Community Edition is a free and open source webbased customer rela Hacking Tutorial, Tips and Tricks 16Tutorial RomHacking. 18Tutorial Intrusion systme et protection. 153Tutorial liste de proxy web. 154Tutorial djouer la censure Facebook. Etre anonyme sur Internet Jai essay de rendre ce tutorial le plus explicite possible pour rpondre. The latest Tweets from Hacking Tutorial (@HackingTut). Ethical Hacking Tutorial, Tips and Trick Learn How to Hack Tutorial, Hacking Tips and Trick. such as your city or precise location, from the web and via thirdparty applications. You always have the option to delete your Tweet location history. Copyright 2006 WhiteHat Security, inc. Worms 28 MySpace (Samy Worm) first XSS worm loggedin user views samys profile page. The hacking tutorial for today is about 3 Steps GMail MITM Hacking Using Bettercap. Computer security is improving and getting tough day by days, but most of technology leave the users behind about the importance of awareness of the user itself. This list is for anyone wishing to learn about web application security but do not have a starting point. You can help by sending Pull Requests to add more information. Web Hacking Immunity's Web Hacking course focuses on understanding common web hacking techniques by having students exploit vulnerable systems. Security professionals with some hands on web hacking experience will get the most out of this course. Ethical Hacking Tutorial PDF Version Quick Guide Resources Job Search Discussion Hacking has been a part of computing for almost five decades and it is a very broad discipline, which covers a. This tutorial in the category Wordpress hacking will teach you how to scan WordPress websites for vulnerabilities, enumerate Wordpress user accounts and brute force passwords. Enumerating WordPress users is the first step in a brute force attack in order Learn Ethical Hacking Download Free Hacking Tools This is an Ethical Hacking Website or Blogs for all. This site offers you all Tips and Tricks to protect your computer. 0x2 Exploit Tutorial: Web Hacking with Burp Suite. Web Application Testing Overview: Web application vulnerabilities offer a large amount of risk to enterprise systems. Many web application vulnerabilities are a result of lack of input sanitization to the web application. Web hacking 101 is an amazing beginners guide to breaking web applications as a bug bounty hunter. All sections of the book are backed up by references from actual publicly disclosed vulnerabilities. The focus on the unique findings for each category will more than likely teach some new tricks. These all books based on ethical hacking tutorials not for hacking. Download Free Collection of Hacking ebook in pdf format All Hacking books in PDF format best hacking books pdf free download. Download Prophet Hacker Blog Book for All type of Hacking (updated android hacking Edition) Hack Forums is the ultimate security technology and social media forum. If you have a hacking tutorial please post it here for consideration to be in the Premium Hacking Tutorials. functions, and development discussions we ask you post here. PHP is the# 1 used web language and is easy to use. Its strength is its simplicity. An Ethical Hacker exposes vulnerabilities in software to help business owners fix those security holes before a malicious hacker discovers them. In this course, you learn all about Ethical hacking with loads of live hacking examples to make the subject matter clear. A couple years ago we did a tutorial on Hacking Tutorials on how to install the popular vulnerability assessment tool OpenVAS on Kali Linux. Weve covered the installation process on Kali Linux and running a basic scan on the Metasploitable 2 virtual machine to identify vulnerabilities. About this Tutorial Hacking has been a part of computing for almost five decades and it is a very broad discipline, which covers a wide range of topics. ETHICAL HACKING web server and its associated software such as databases and other interfaces. is a legal and safe network security resource where users test their hacking skills on various challenges and learn about hacking and network security. Also provided are articles, comprehensive and active forums, and guides and tutorials. Hacking Hacking Exposed 6: Network Security Secrets Solutions McClure Scambray 544 Hacking Exposed 6: Network Security Secrets Solutions N early synonymous with the modern Internet, the World Wide Web has become a ubiquitous part of everyday life. Widespread adoption of highspeed Internet In this tutorial, well take a look at how we can hack into a webcam secretly and remotely over the internet and take a peek at whats going on at the other side. This is the page of Web App Hack tutorial. Here you can start this hackme, or leave a comment. Focus on the right bar to see the statistics related or to browse the other hackmes associated with the categories and tags related. Here is a collection of Best Hacking EBooks PDF 2018. Download Hacking Books In PDF and learn best hacking tutorials 2018. There are many ways to Learn Ethical Hacking like you can learn to hack from online websites, learn from Hacking books. Learn web penetration in easytouse ISOs. Boot our ISO and start hacking. Our exercises are not just a set of vulnerabilities, they are built to teach you how to think like an attacker. PentesterLab is an easy and great way to learn penetration testing. PentesterLab provides vulnerable systems that can be used to. Learn Hacking on DarkDeep Web by an anonymous tutorial. Prevent deep web hacking from the hacker. Follow news, communities and forum to learn the ethics Use SELECT userid, username, password, email FROM users WHERE userid'1' Note: It is bad to store plaintext passwords, use a passwordbased key derivation function like PBKDF2 or bcrypt. Hacking is identifying weakness in computer systems or networks to exploit its weaknesses to gain access. Example of Hacking: Using password cracking algorithm to gain access to. Hi, welcome to our web hacking and security course. In this course, we will teach you how client based, server based and application based web attacks are performed in a. How To: Successfully Hack a Website in 2016! By MrNakup3nda; 1416 7: 01 PM in case you do not know you can see my tutorial on how to use google to hack. That will help to get the attention of the web host in question. As for hacking the website that has your compromised content. That's usually pretty much impossible, particularly if. Deep Web Hacking Tutorial If you need to learn more about the deep web hacking, then you must follow my complete tutorial instruction. Hacking Web Services by Shreeraj Shah. This is the first book of its kind Steps in Web Services Hacking Ive broken this tutorial down into 4 steps: 1. ) Learn as much as you can about the system 2. Copyright (C) 2013, Your Challenge 41 Task 1: latitude 41. Travis doesn't know the number of the bus he Learn how to do ethical hacking, penetration testing, web testing, and wifi hacking using kali linux! 3 (20, 564 ratings) Course Ratings are calculated from individual students ratings and a variety of other signals, like age of rating and reliability, to ensure that they reflect course quality fairly and accurately. What is the Best Way to Learn Hacking for Beginners? Consider the following steps: . am big interst for hacking tutorial. Hello dudes i want to become a hacker but i dont no about hacking how to hack any web site so can you help me. A lot of people (including me before doing research for this article) think that they can become a hacker using some free hacking tools available on web. Its true that some common types of hacking can be easily done with help of tools, however doing it does not really make you a hacker. Before starting the tutorial on Website Hacking you should know the working of web application first. How the web server and web application works together. Well Web application is the program or software that can be accessed over the internet. In general we called web application as a website. Di kesempatan lalu, saya pernah posting di blog ini tentang tutorial Hacking Anatomy (Plus Real Hacking Example). Untuk kesempatan kali ini saya akan posting studi kasus security hole di layer aplikasi yang dapat berimplikasi terhadap keamanan OS server nya. Web Hacking Tutorial DNS HackingHijacking (Tutorial) This is an introduction to DNS poisoning which also includes an example of quite a nifty application of it using the IP Experiment. Huge List of Darknet (Deep Web) Hidden Websites 2016: Hello! guys so today i will be sharing HUGE list of Darknet (Deep Web) hidden This tutorial is for educational purposes, we learn to hack to understand how hackers work, to make our own web application more secure. Web security is an important factor when developing web apps. Also, the prereqs listed above are for the entire web pentesting series, and most probably you'll be able to follow this tutorial without completing some of them, since. GBHackers on Security is Advanced Persistent Cyber Security Online platform which including Cyber Security Research, Web Application and Network Penetration Testing, Hacking Tutorials, Live Security Updates, Technology updates, Security investigations With dedicated Cyber security Expert Team and help to community more secure..
-
Related Images: